There's no denying that data breaches can wreak havoc on your organization, leading to financial losses and damage to your reputation. In this comprehensive guide, you will learn effective strategies and practical steps to safeguard your sensitive information from potential threats. By implementing these techniques, you can enhance your cybersecurity posture and keep your data secure. Let's explore the imperative actions you can take to prevent costly data breaches and protect your assets.
The Costly Consequences of Data Breaches
Data breaches not only expose sensitive information but also trigger a range of repercussions that can cripple an organization. From immediate financial penalties to long-term effects on brand reputation, the fallout from a breach can be extensive. Companies may find themselves facing legal challenges, compliance costs, and increased regulatory scrutiny, all of which threaten to derail business operations and divert resources from core functions.
Financial Ramifications for Businesses
Financial losses stemming from data breaches can be staggering. The average cost of a data breach in 2023 was estimated at $4.35 million, which encompasses factors like detection, response, and the potential loss of business due to interrupted operations. You may also incur fines, legal fees, and the costs of implementing new security measures. These expenses can significantly impact your bottom line, especially if your company is small or mid-sized.
Reputational Damage and Lost Customer Trust
Data breaches can severely damage your brand's reputation, leading to diminished customer loyalty and trust. Many consumers are reluctant to engage with businesses that have experienced a breach, fearing for their own data security. Research indicates that 78% of consumers would stop doing business with a company that has experienced a data breach. Once lost, these relationships can be challenging to rebuild, particularly in industries where trust is paramount, such as finance and healthcare.
Rebuilding your reputation post-breach requires consistent effort, transparency, and dedicated outreach to restore customer confidence. Implementing effective communication strategies during and after the incident can mitigate damage, but the challenge lies in proving your commitment to data security through actionable measures. Engaging in customer education about your data protection practices can further help in regaining trust. Recovery may take years, but investing in security improvements and customer assurance can gradually pave the way for a healthier relationship with your clientele.
The Psychological Tactics Cybercriminals Employ
Cybercriminals harness psychological tactics to exploit vulnerabilities in your organization, often targeting human emotion and cognitive biases. By understanding how people think and react, they manipulate individuals into making poor decisions, ultimately leading to successful data breaches. Techniques such as urgency, fear, or even trust can be weaponized to deceive employees, making them more susceptible to phishing and social engineering attacks.
Manipulating Human Behavior for Breach Success
Human behavior is often predictable, and cybercriminals take full advantage of this predictability. They design scams that leverage urgency or fear, prompting impulsive actions without careful consideration. For example, a phishing email may create a false sense of alarm, instructing you to verify your account immediately or risk losing access. In such high-pressure situations, the temptation to act quickly often outweighs the instinct to pause and assess the credibility of the request.
Recognizing and Combating Social Engineering Techniques
Identifying social engineering tactics can significantly reduce the risk of falling victim to cyber threats. Cybercriminals often employ technology that mimics trusted entities, such as emails from financial institutions or messages that seem to come from colleagues. Training your workforce to recognize these red flags—like unexpected requests for sensitive information or unusual communication channels—can empower them to refuse manipulation and report suspicious activities.
To combat social engineering, foster a culture of skepticism where employees feel empowered to question the legitimacy of unexpected communications. Regular training sessions highlighting real-life examples of social engineering attacks can enhance awareness and reinforce the importance of verifying requests through independent channels. Encouraging your team to adopt a habit of double-checking can diminish the effectiveness of these psychological tactics, thereby bolstering your organization's overall security posture.
Building a Robust Defense Strategy
Establishing a robust defense strategy begins with identifying your data assets and understanding the potential risks associated with them. Implementing layered security measures, such as firewalls, encryption, and access controls, ensures that your sensitive information remains protected. Regularly updating software and systems can help close vulnerabilities before they're exploited. Crafting an incident response plan is equally important, allowing you to minimize damage and recover quickly if a breach does occur. This proactive approach not only protects your data but also builds trust and confidence with clients and stakeholders.
Crafting a Comprehensive Data Protection Policy
A comprehensive data protection policy outlines how your organization manages sensitive information. It should clearly define data classification, storage, access rights, and protocols for data sharing. Additionally, it's vital to include guidelines on data retention and destruction practices, ensuring compliance with legal and regulatory requirements. Regular assessments and updates to this policy will keep your organization aligned with evolving threats and technologies.
The Role of Employee Training and Awareness
Integrating a culture of data protection through employee training is a game-changer in preventing breaches. Regular training sessions should focus on recognizing phishing attempts, the importance of strong passwords, and adhering to your data protection policy. This empowers your team to act as the first line of defense against cyber threats.
The effectiveness of your training hinges on engaging employees in interactive sessions that reflect real scenarios they may encounter. Incorporating simulations for phishing attacks not only raises awareness but also fosters a sense of responsibility among your staff. Studies show that companies that invest in employee cybersecurity training can reduce the likelihood of a data breach by as much as 70%. Creating an environment where employees feel confident to speak up about security concerns is vital for cultivating an agile and responsive data protection culture.
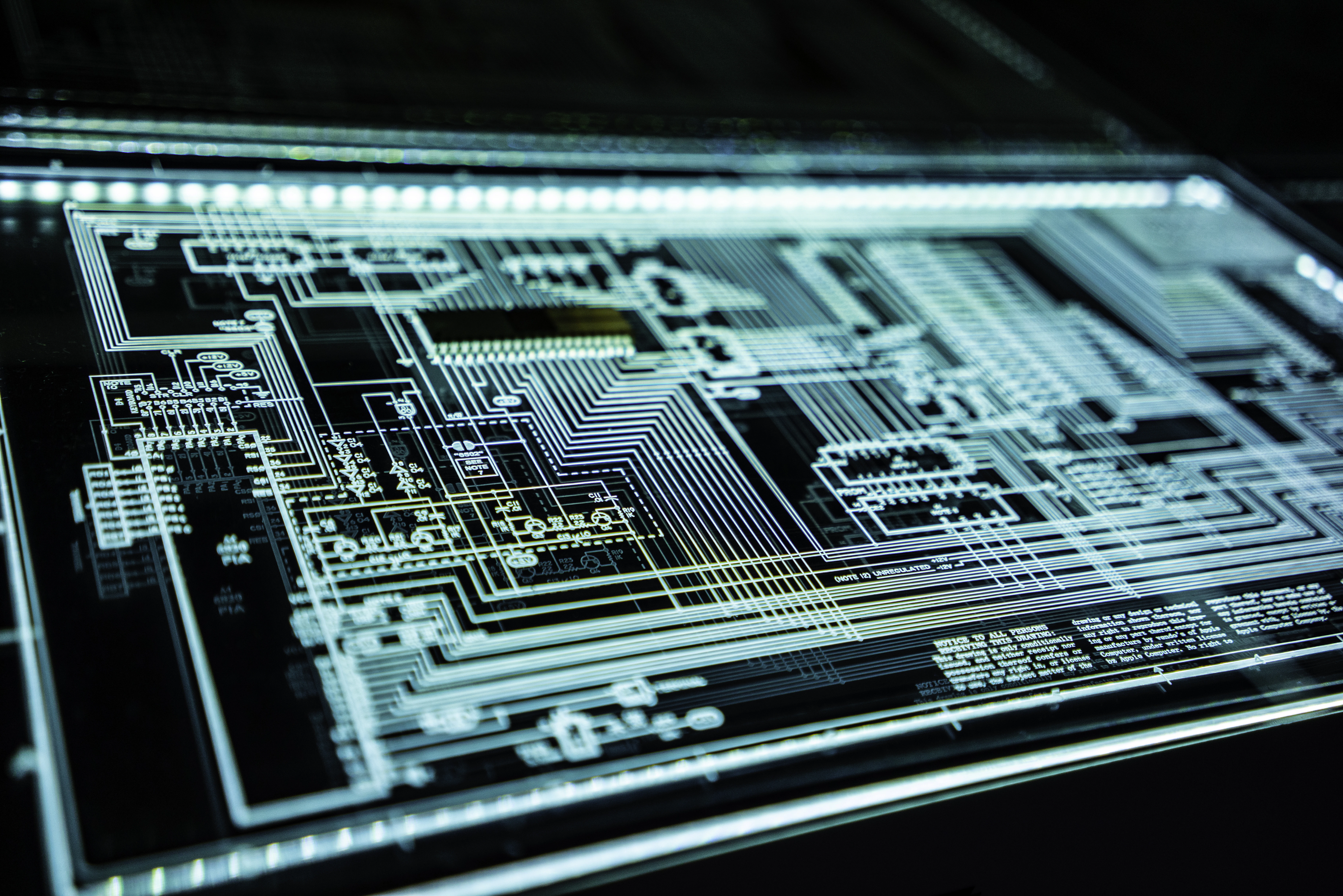
The Technological Arsenal: Tools and Techniques
Your defense against data breaches hinges not just on policies but also on a solid technological framework. Implementing the right mix of tools and techniques can significantly bolster your business's security posture. From firewalls to encryption, ensuring your technological arsenal is up-to-date will empower you to defend against emerging threats effectively.
Essential Security Software for Every Business
Best Practices for Regular Software and System Updates
Proactive Monitoring and Incident Response Plans
Your ability to prevent data breaches heavily relies on proactive monitoring and having a well-defined incident response plan. Continuous vigilance enables you to detect unusual activities early, while a structured response protocol ensures that when incidents do occur, your organization can act decisively and efficiently to minimize damage.
Setting Up Real-Time Monitoring Systems
Implementing real-time monitoring systems allows you to track system activity and user behavior relentlessly. By utilizing advanced security information and event management (SIEM) tools, you can sift through vast amounts of data to identify anomalies that may indicate a breach. This early detection often serves as your first line of defense, enabling you to respond before threats escalate.
Crafting an Effective Incident Response Protocol
An effective incident response protocol lays the foundation for a swift reaction when a data breach occurs. Begin by clearly defining roles and responsibilities among your team. This should include a communication plan to keep stakeholders informed and an established procedure for documenting the incident. Your response strategy should cover everything from containment and eradication of the threat to post-incident analysis and recovery plans, helping to fortify defenses against future attacks.
Crafting this protocol requires collaboration with key stakeholders across departments, ensuring that everyone understands their part in the process. Prioritize regular training simulations to keep your team sharp and aware of potential scenarios they may face. Incorporate insights from previous incidents, both your own and those within your industry, to refine your approach continuously. A well-prepared team can significantly reduce recovery time and potentially avert compliance penalties, thus safeguarding your organization's reputation and financial stability.
Final Words
On the whole, safeguarding your data is a responsibility that shouldn't be overlooked. By following the step-by-step guidelines outlined in this guide, you can significantly mitigate the risk of costly data breaches. Implementing strong security measures, staying informed about potential threats, and fostering a culture of security within your organization will empower you to protect your sensitive information effectively. Being proactive today will save you from significant repercussions tomorrow.