Just because you're operating on a small to medium-sized business budget doesn't mean you can't adopt a robust zero-trust architecture. In this guide, you will learn practical steps to secure your network by verifying every user and device, regardless of their location. We'll explore cost-effective strategies that enable you to enhance your cybersecurity posture without breaking the bank. Follow these recommendations to implement a zero-trust model that protects your assets and data effectively.
Identifying Vulnerabilities: The First Step to Zero-Trust
Identifying vulnerabilities within your organization lays the groundwork for a successful zero-trust implementation. Begin by evaluating your current security posture to uncover weaknesses that could be exploited by malicious actors. Systemic gaps, outdated software, and unaccounted-for access points can undermine your efforts. Once these vulnerabilities are identified, you can prioritize their remediation and bolster defenses effectively.
Conducting a Risk Assessment
A risk assessment involves evaluating both technical and non-technical factors that contribute to your organization's overall security. Consider threats from both internal and external sources, the potential impact of a breach, and the likelihood of various attack scenarios. Establishing a clear understanding of risk can inform how to allocate resources and address vulnerabilities aligned with your business priorities.
Mapping Data Flows and User Access
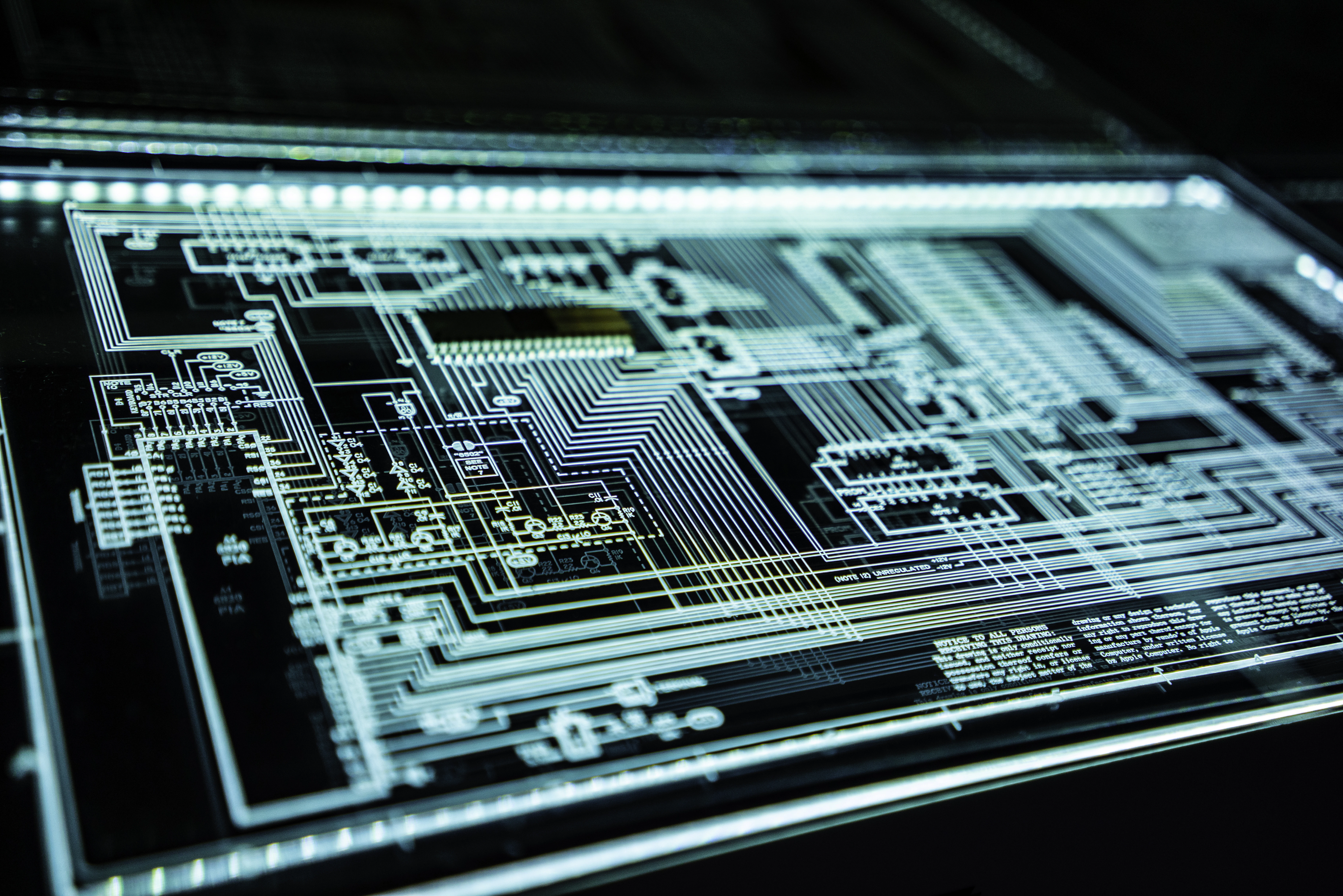
Mapping data flows and user access allows you to visualize how information moves through your organization and who has access at each point. This process helps in identifying critical assets, potential exposure during data transfer, and unauthorized access. By clearly defining user roles and permissions, you can implement strict access controls that align with zero-trust principles.
In detail, this mapping process involves creating a comprehensive inventory of data types, where they are stored, and how they are accessed by users or systems. Generate flowcharts depicting interactions among users, applications, and devices that handle sensitive data. This visual representation reveals patterns and inefficient access points, enabling you to segment your network and limit exposure to unauthorized users. Automation tools can assist in maintaining this map, ensuring it evolves alongside your organization's growth and changes in access protocols.
Core Principles of Zero-Trust in Action
Implementing a zero-trust architecture revolves around key principles that prioritize security at every level, ensuring that no user or device is automatically trusted. Each access request must undergo verification, regardless of its origin, fostering an environment where maintaining security is a continuous, proactive effort. By applying the principle of least privilege, organizations limit user permissions exclusively to what is necessary for their role, significantly reducing the attack surface. Frequent monitoring and continuous learning from security incidents also play vital roles, further reinforcing the unique framework that zero trust provides.
User Identity Verification: Beyond Passwords
Enhancing user identity verification moves beyond traditional passwords into multi-factor authentication (MFA) and behavioral analytics. MFA adds layers of security by requiring users to provide additional evidence of identity—like a one-time code sent to a mobile device—before granting access. Behavioral analytics assesses user actions in real-time, identifying anomalies based on a user's patterns, effectively flagging potential threats before they escalate.
Device and Endpoint Security: Ensuring Trustworthiness
To ensure trustworthiness, focus on rigorous device and endpoint security measures. Every device connected to your network should be validated against strict security protocols, including up-to-date antivirus software and encryption. Regular audits of device compliance can help identify vulnerabilities, while implementing network segmentation can limit access and mitigate risks associated with compromised devices.
Consider adopting solutions like Mobile Device Management (MDM) to enforce security policies on mobile devices, which often present higher risks. By enforcing device encryption, remote wipe capabilities, and secure access protocols, you establish a solid foundation for endpoint security. For instance, allowing only managed devices into your network ensures that unverified equipment cannot access sensitive information, thereby minimizing the impact of potential breaches. Regularly reviewing and updating these measures keeps your defenses strong in a rapidly evolving threat landscape.
Implementing Scalable Solutions on a Budget
Scaling your zero-trust architecture doesn't have to drain your budget. Focus on incremental implementations that align with your current infrastructure and business needs. Start with pilot projects to test effectiveness and expand gradually, ensuring that each step remains financially viable while addressing security gaps. This phased approach allows you to achieve long-term goals without overspending, making adjustments based on real-world feedback and evolving requirements.
Cost-Effective Tools and Technologies
Utilizing open-source or affordable commercial tools can significantly reduce costs while implementing zero-trust principles. Solutions like VPN alternatives, access management systems, and endpoint security software are available at various price points. Prioritize those that offer imperative features compatible with your existing systems. Regularly assess vendor offerings for competitive pricing and features, ensuring you leverage the best value without sacrificing security.
Leveraging Existing Infrastructure for Zero-Trust
Your current infrastructure can serve as a strong foundation for a zero-trust architecture. Assess existing hardware and software capabilities to identify any built-in security features like firewalls, network segmentation, and access controls. Integrating these tools can optimize investments while bolstering security. Incremental upgrades, rather than complete overhauls, can maintain performance while enhancing protection.
For instance, if your organization already uses multi-factor authentication (MFA) for remote access, enhance its effectiveness by applying the same principles internally. Review existing firewall configurations to segment your network and minimize lateral movement risks. By utilizing tools you already have, you can implement a zero-trust strategy efficiently while avoiding unnecessary expenditures on new solutions. This strategy not only preserves your budget but also familiarizes your team with the security mechanisms in place, facilitating smoother transitions and greater compliance with zero-trust policies.
Building a Culture of Security Awareness
A robust culture of security awareness empowers your team to recognize and respond effectively to threats. By integrating security into daily operations and decision-making, you foster an environment where every employee understands their role in maintaining security. Regular communication about potential risks, combined with visible support from leadership, creates a unified approach to safeguarding company assets and customer data, ultimately contributing to a more resilient organization.
Employee Training: The Human Element in Zero-Trust
Employee training is fundamental in creating a zero-trust environment. You should conduct regular workshops that cover topics such as phishing, password management, and social engineering tactics. Tailor these sessions to be engaging and interactive, incorporating real-life scenarios relevant to your organization. Additionally, quizzes or simulations can reinforce learning, ensuring your team remains vigilant and informed about emerging threats.
Promoting a Security-First Mindset Across Teams
Embedding a security-first mindset into your company culture requires ongoing collaboration and communication among teams. Encourage cross-departmental initiatives where team members share security best practices and threat experiences. Create recognition programs that reward employees who identify potential vulnerabilities or suggest improvements. Regularly discussing security in team meetings keeps the topic top-of-mind, allowing employees to view security not merely as a responsibility but as an integral part of their roles, ultimately creating a more secure organizational culture.
Organizations that prioritize a security-first mindset foster a proactive culture around cybersecurity. For instance, a study by Ponemon Institute found that companies with well-educated employees can reduce the risk of data breaches by 30%. By integrating security discussions into regular meetings and celebrating security champions within your teams, you encourage open dialogue about vulnerabilities and best practices. This collaborative approach ensures that security is viewed not as a burden but as a shared goal, empowering employees to take collective responsibility in safeguarding sensitive information.
Measuring Success: KPIs for Zero-Trust Deployment
Success in implementing a zero-trust architecture can be quantified through specific key performance indicators (KPIs). Track metrics such as incident response time, breach attempts blocked, and user authentication failures to gauge effectiveness. Additionally, assess end-user training completion rates and phishing simulation results. These KPIs enable you to evaluate your security posture over time, ensuring that your zero-trust strategy evolves to meet emerging threats.
Continuous Monitoring and Improvement
Continuous monitoring is crucial for maintaining the efficacy of your zero-trust framework. Regularly review access logs, user behavior analytics, and threat intelligence feeds to identify anomalies. Employ automation tools to facilitate real-time insights that inform necessary adjustments, keeping your security measures aligned with evolving risks. Ongoing improvements based on monitoring findings fortify your defenses.
Reporting and Adjusting Strategies Based on Outcomes
Establishing a feedback loop through regular reporting enhances your zero-trust deployment. Analyze the data collected from your KPIs to identify patterns, strengths, and weaknesses. Use these insights to refine your security strategies, such as adjusting access controls or retraining employees. This proactive approach fosters a dynamic security environment, ensuring your organization remains resilient against threats.
Continuous assessment of your security measures involves detailed reporting that highlights the effectiveness of your zero-trust implementation. You can create quarterly reports summarizing incident responses, detection rates, and user compliance. By sharing these findings with your team, you promote accountability and encourage a collaborative approach to security improvements. Adjustments based on performance metrics can lead to enhanced policies and procedures, ensuring your zero-trust architecture adapts seamlessly to new challenges.
Summing up
From above, implementing a Zero-Trust Architecture on an SMB budget requires strategic planning and resourcefulness. You should prioritize identifying and classifying your assets, segmenting your network, and enforcing strict access controls. Leverage cost-effective solutions, such as cloud services and open-source tools, to enhance your security posture without overspending. Regularly evaluate and update your security protocols to align with evolving threats. By taking these steps, you can protect your organization effectively while adhering to budget constraints.